President Erika D. Beck speaking at the The Camarillo Chamber of Commerce CI Connection Luncheon pic.twitter.com/U71BPZMvH0
— CSU Channel Islands (@csuci) February 15, 2018
Category: Showcase
I will be giving a talk on Cybersecurity for small businesses on December 8
Detective Kimo Hildreth and I will be giving a talk at a breakfast event on Cybersecurity for Small Businesses on Friday December 8, 2017, at 8:30am. To RSVP and view more event details click here. The event is organized by Assemblymember Jacqui Irwin, and it will take place at 2100 Thousand Oaks Blvd, in the “Oak and Park Room”.
msoltys-talk-dec8-2017First CS Advisory Board meeting
The first Computer Science Advisory Board meeting will take place on November 3.
Time, Location and Parking
- November 3rd (.ics calendar invite)
12pm-1:30pm - At the Broome Library, J. Handel Evans Conference Room
- Given the time of day, a buffet lunch will be provided.
- The A6 parking lot will be reserved specifically for CI guests attending this meeting.
Agenda
- Introductions & Lunch
- Presentation – Computer Science and Mechatronics
- Discussion
Presentation Slides
AdvisoryBoard-Nov2017Pictures from the event
Chairs Meeting
CSU CS/IS/SE/IT/CE Chairs Meeting
Organizers:
- Michael Soltys, michael.soltys@csuci.edu
- Melissa Danforth, mdanforth@csub.edu
- This Page:
http://www.msoltys.com/csu-chairs-2017/
Time, Place & Wifi:
- October 27, 2017, 9:30am to 4:30pm
- CSU Channel Islands, John Spoor Broome Library, 2nd Floor (J.H.Evans BRO 2533) Conference Room
- Parking: You can use your CSU institution parking permit at CI: A2 lot is a good place to park; parking can be a challenge at CI, but Fridays tends to be easier.
- WiFi: You can use Eduroam, or the “CI” SSID with login: solutionGuest and password: SolutionCenter
- Suggested hotel: 4994 Verdugo Way, Camarillo, CA 93012
Material:
- PDF of the Agenda.
- Short link to this page: http://www.msoltys.com/csu-chairs-2017.
- Minutes from previous meeting, which was held on March 25, 2016, Cal Poly Pomona – thank you Melissa Danforth for taking notes and transcribing them.
- SB 412 and SB 1440
- EO 1110 and EO 1100
- A very helpful document from Suzanne Rivoire (suzanne.rivoire@sonoma.edu) regarding the computing GE’s on CSU campuses.
- Minutes from the meeting (thank you Melissa Danforth!)
dinner
- 6pm at Bistro 13 near the Hotel
- It will be a “no-host” dinner with a everyone paying their own tab.
- Dinner was originally scheduled at the Safire restaurant, but it was closed with an eviction notice when we got there 🙂
Photos
iSprinkle – a topical capstone project @CSUCI @cagomez805
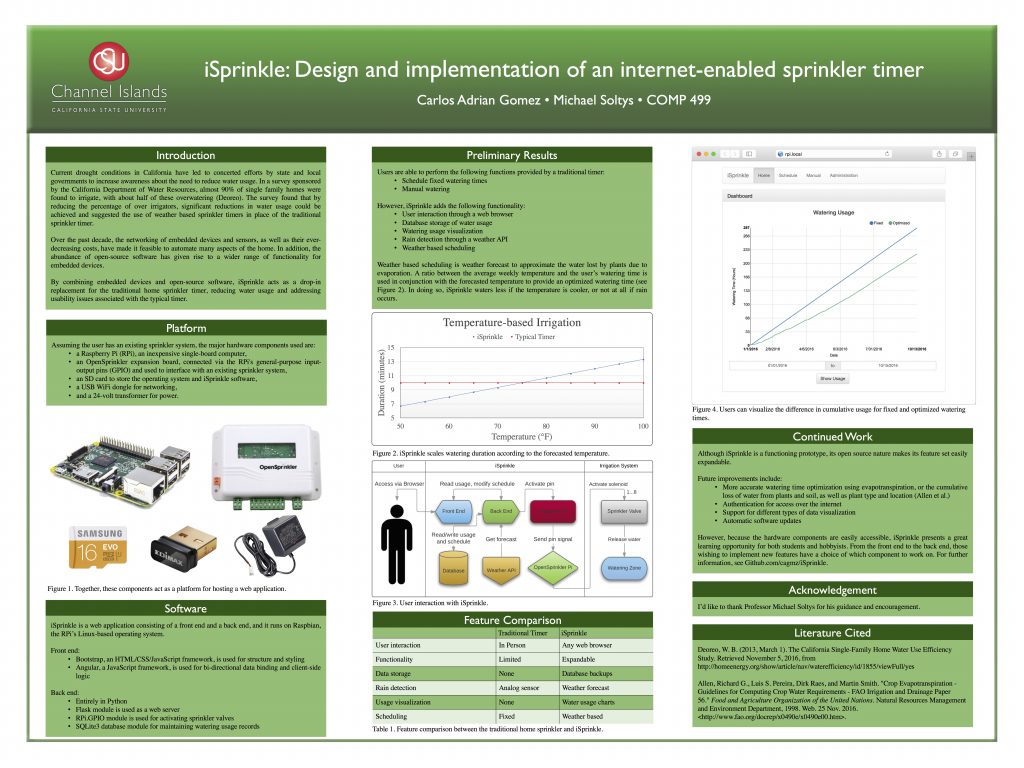
 iSprinkle is a Raspberry Pi powered irrigation controller which will allow a user to set an initial irrigation schedule for a sprinkler system using a web interface, after which it will use the local weather forecast to adjust the base watering schedule as needed. iSprinkle is the result of a senior Capstone project (COMP499) at California State University Channel Islands, undertaken by student Carlos Gomez in 2016, advised by Michael Soltys. A detailed write up of the project, where we partnered with Prof. Adam Sędziwy (who visited CI in June 2016), can be found here:
iSprinkle is a Raspberry Pi powered irrigation controller which will allow a user to set an initial irrigation schedule for a sprinkler system using a web interface, after which it will use the local weather forecast to adjust the base watering schedule as needed. iSprinkle is the result of a senior Capstone project (COMP499) at California State University Channel Islands, undertaken by student Carlos Gomez in 2016, advised by Michael Soltys. A detailed write up of the project, where we partnered with Prof. Adam Sędziwy (who visited CI in June 2016), can be found here:
- iSprinkle: Design and implementation of an internet-enabled sprinkler timer, by Carlos Adrian Gomez, Adam Sedziwy and Michael Soltys.
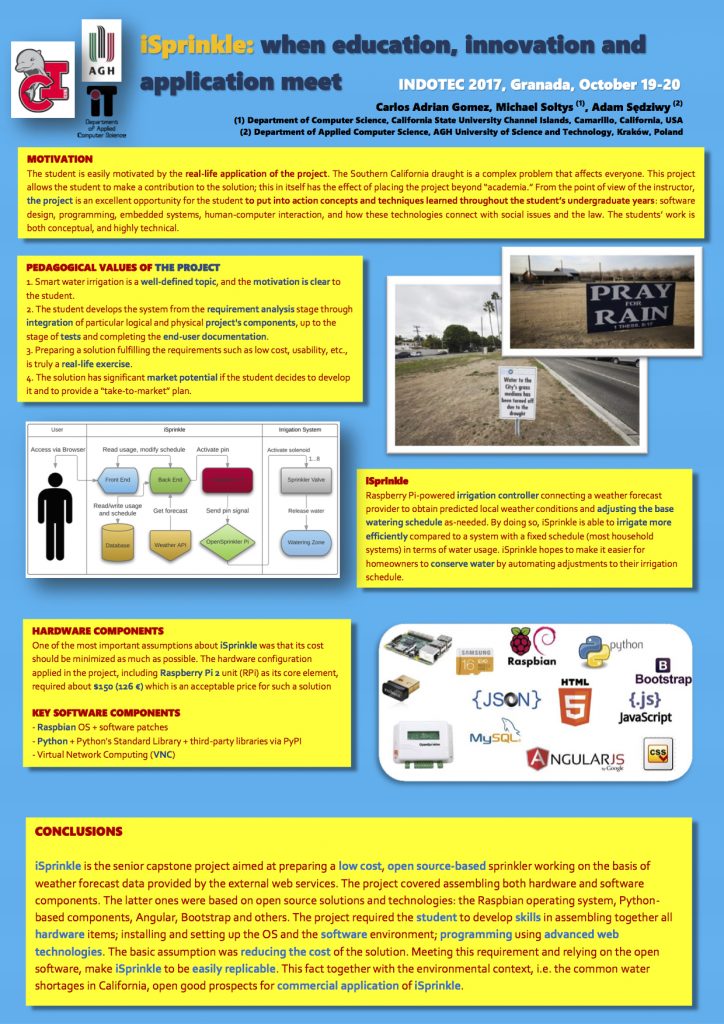
A short version of the above paper will be presented at INDOTEC2017:
- iSprinkle: when education, innovation and application meet, by Carlos Adrian Gomez, Adam Sedziwy and Michael Soltys, to be presented at the 5th International Conference on Educational Innovation in Technical Careers, INDOTEC 2017.
iSprinkle was also presented at SCCUR 2016, the Southern California Council for Undergraduate Research Conference at UC Riverside on November 12, 2016.
The design of a system such as iSprinkle requires a holistic approach that is very different from most class assignments. The former usually span a few files that are to be turned in within a week or two, making it difficult to implement a system with many “moving parts.” However, iSprinkle’s functionality is divided between the front-end and back-end, both of which need to communicate so that the user’s requests are fulfilled. Designing such a system requires taking into consideration many aspects; from major decisions such as deciding on a backend language to use, to minutiae such as the date and time formats to use across the backend and front end to maintain consistency.
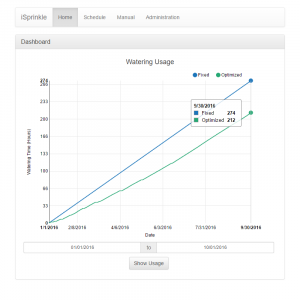 By doing so, iSprinkle will be able to irrigate more efficiently compared to a fixed schedule; by progrmmatically modifying the user’s watering schedule, iSprinkle will increase/decrease the amount of watering that the schedule dictates depending on data that it receives from a weather API. iSprinkle hopes to make it easier for homeowners to conserve water by automating adjustments to their irrigation schedule.
By doing so, iSprinkle will be able to irrigate more efficiently compared to a fixed schedule; by progrmmatically modifying the user’s watering schedule, iSprinkle will increase/decrease the amount of watering that the schedule dictates depending on data that it receives from a weather API. iSprinkle hopes to make it easier for homeowners to conserve water by automating adjustments to their irrigation schedule.
 Carlos Adrian Gomez has since graduated from CI, and is working as a Software Engineer in the Ventura area.
Carlos Adrian Gomez has since graduated from CI, and is working as a Software Engineer in the Ventura area.
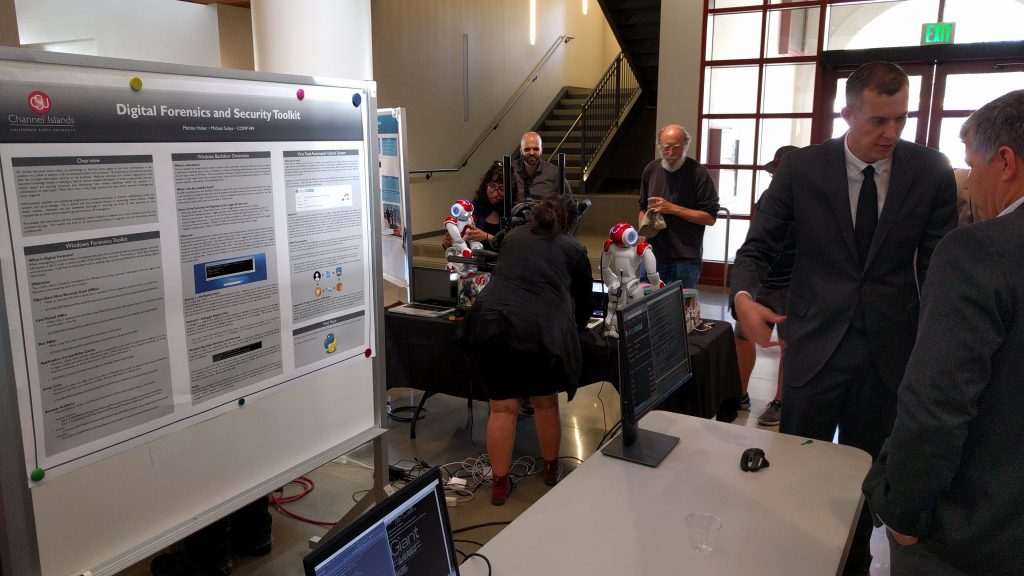
CI Computer Science students build a digital forensic tool
 On August 7, 2017, the CI Computer Science students presented a prototype of a digital forensic tool, which we named SEAKER (Storage Evaluator and Knowledge Extraction Reader), as part of their Masters COMP 524 Cybersecurity course. This project was a collaboration between the Ventura County District Attorney (VCDA) Digital Forensics Lab and CI Computer Science, under the umbrella of the SoCal High Technology Task Force (HTTF).
On August 7, 2017, the CI Computer Science students presented a prototype of a digital forensic tool, which we named SEAKER (Storage Evaluator and Knowledge Extraction Reader), as part of their Masters COMP 524 Cybersecurity course. This project was a collaboration between the Ventura County District Attorney (VCDA) Digital Forensics Lab and CI Computer Science, under the umbrella of the SoCal High Technology Task Force (HTTF).
The students presented a live demo with devices supplied by the Ventura County DA. The SEAKER prototype was able to compile search results in less than a minute depending on the size of the device. According to VCDA officials at the presentation this is a remarkable increase in efficiency and will be a useful tool in the field: while imaging of a hd can take up to 4 hours, SEAKER performs a triage search in minutes.
Digital Forensics (DF) deals with the recovery and investigation of clues from digital devices (computers, handhelds, iPads, routers, modems, DVRs, etc.). The goal of this effort is to support or refute a hypothesis in court. DF is a complex and technical field: it can be used to attribute evidence to specific suspects, confirm alibis or statements, determine intent, identify sources, or authenticate documents.
A DF investigation commonly consists of 3 stages: acquisition or imaging of exhibits, analysis and reporting. The SEAKER tool helps with the acquisition of data from digital devices in a way that prevents tampering.
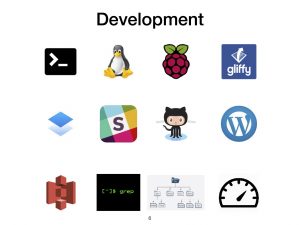 The SEAKER project was a fantastic learning experience for our students, as its design and prototyping combined many different skills: The C programming language, BASH shell scripting, the Linux Operating Systems and command line, the Raspberry Pi hardware, Gliffy diagrams, Dropbox Paper (which we used as a Wiki); Slack collaborative discussion / brainstorming tool, the GitHub software repository which was used as a collaborative tool in the design of the software that animated the Raspberry Pi, WordPress blogging, AWS S3 which served as a repository of the final product, Grep (regular expressions and pattern matching), working with different file systems, and of course strict performance (speed, read only). All of this had to be combined by a group of 18 students, with different backgrounds and skill sets to produce something that could be used by DF examiners.
The SEAKER project was a fantastic learning experience for our students, as its design and prototyping combined many different skills: The C programming language, BASH shell scripting, the Linux Operating Systems and command line, the Raspberry Pi hardware, Gliffy diagrams, Dropbox Paper (which we used as a Wiki); Slack collaborative discussion / brainstorming tool, the GitHub software repository which was used as a collaborative tool in the design of the software that animated the Raspberry Pi, WordPress blogging, AWS S3 which served as a repository of the final product, Grep (regular expressions and pattern matching), working with different file systems, and of course strict performance (speed, read only). All of this had to be combined by a group of 18 students, with different backgrounds and skill sets to produce something that could be used by DF examiners.
 One of the CI pillars is Community Engagement and Service Learning. This approach identifies needs in the community, and builds a curriculum around research and development to address those needs. The SEAKER project is a great example of such a symbiotic relation between CI and the community. Also, it is an example of the strength of a pedagogical approach that combines both theory and practice. Without theory a field becomes a collection of ad hoc procedures. But without practice theory becomes an abstract exercise in intellectual virtuosity. We plan to build on the approach that combines the Service Learning and Theory & Practice paradigms as we go forward with our Computer Science program in Security Systems Engineering and our Masters level offering in Cybersecurity.
One of the CI pillars is Community Engagement and Service Learning. This approach identifies needs in the community, and builds a curriculum around research and development to address those needs. The SEAKER project is a great example of such a symbiotic relation between CI and the community. Also, it is an example of the strength of a pedagogical approach that combines both theory and practice. Without theory a field becomes a collection of ad hoc procedures. But without practice theory becomes an abstract exercise in intellectual virtuosity. We plan to build on the approach that combines the Service Learning and Theory & Practice paradigms as we go forward with our Computer Science program in Security Systems Engineering and our Masters level offering in Cybersecurity.
Some photos from the event:
Mechatronics Engineering at CSUCI
an information talk
overview
 The Department of Computer Science at CSU Channel Islands is delighted to announce that we will be starting a new program in Mechatronics Engineering in 2018.
The Department of Computer Science at CSU Channel Islands is delighted to announce that we will be starting a new program in Mechatronics Engineering in 2018.
We will be taking in the first group of 24 students in the fall of 2018, and growing the program by a new cohort of 24 students every year after that, for a total of just under 100 students thereafter.
CSUCI’s news release and landing page:
- https://www.csuci.edu/news/releases/2017-mechatronicsengineering.htm
- https://www.csuci.edu/academics/mechatronics.htm
In the local news:
- Moorepark Acorn (July 15, 2017)
- CI news release (July 17, 2017)
- The Camarillo Acorn and Simi Valley Acorn (July 21, 2017)
- Noozhawk (July 21, 2017)
Alternative (short) links to this page:
The CI Mechatronics program has been assigned, by the Chancellor’s Office, the following:
- CSU degree-program code:
09102 - CIP code:
14.4201
Mechatronics Zoom meeting on Tuesday, Nov. 7 at 6:00 p.m.; to register
Mechatronics Flyer:
What is Mechatronics?
Mechatronics is a fast growing area of Engineering that is interdisciplinary by nature, as it combines aspects of Mechanics, Control Theory, Computer Science, and Electronics, in order to improve and optimize the design and functionality of systems, as well as making them more economical and reliable. Industrial robots and drones are quintessential examples of mechatronics systems: they include aspects of electronics, mechanics, and computing. Modern production equipment consists of mechatronic modules that are integrated according to a suitable control architecture. Popular examples include automotive subsystems, including anti-lock brakes and spin-assist, as well as everyday equipment, such as autofocus cameras, video, hard disks and CD players.
The complexity of mechatronics requires at least a bachelor’s degree to get into the field. Although the U.S. Bureau of Labor Statistics (BLS) does not provide specific salary information for mechatronics engineers, it does show that median annual wages for all specialized engineers not categorized was $92,680 as of May 2013. The middle 50% of these professionals earned between $68,610 and $117,930 yearly.
The need for mechatronics at ci
CSU Channel Islands is the only public university in the County of Ventura. The campus is strategically located on the so called “101 Tech Corridor,” sharing the neighborhood with companies such as Amgen, Haas, Teledyne Technologies, HRL Laboratories, and many others, not to mention Point Mugu and Port Hueneme Naval bases, as well as Lockheed, Rocketdyne, and other companies in the greater Los Angeles area. Therefore there is a great need and demand for engineers in the local industry and community.
The local companies strongly support the establishment of an Engineering program on the CI campus, and a comprehensive report was produced in 2013 with recommendation for an engineering degree that would meet the needs of the community. In this report it was noted that Ventura County hires about 290 engineers each year, not to mention that the local Naval Bases send their officers to complete their Engineering degrees across the nation, which results in high costs for the Navy, and a loss of revenue for Ventura County.
Mechatronics curriculum
Note that this is still a provisional curriculum; we may make small changes to it as we are implementing the program for the start date of fall 2018.
| Code | Name | Units | GE | Prerequisites in Place |
| CHEM 105 | Introduction to Chemistry | 3 | No prerequisites | |
| MATH 150 | Calculus I | 4 | 3 | Calculus Placement Exam. or MATH 105 |
| EMEC 121 | Programming in C part 1 | 4 | 3 | MATH 105 or equiv., COMP 105 or permission |
| EMEC 122 | Programming in C part 2 | 4 | EMEC 121 | |
| MATH 250 | Calculus III | 3 | MATH 151 with at least a C | |
| COMP 151 | Data Structures and Program Design | 4 | COMP 150 | |
| COMP 162 | Computer Architecture and Assembly Language | 3 | COMP 150 | |
| MATH/PHIL 230 | Logic and Mathematical Reasoning | 3 | 3 | No prerequisites |
| MATH 240 | Linear Algebra | 3 | MATH 151 | |
| COMP 232 | Programming Languages | 3 | COMP 150, COMP 151, COMP 162 | |
| COMP 262 | Computer Organization and Architecture | 3 | COMP 151, COMP 162 | |
| EMEC 200 | Logic Circuits | 4 | MATH 150, MATH 230, COMP 162 | |
| EMEC 225 | Engineering Design | 3 | EMEC 200 | |
| PHYS 200 | General Physics I | 4 | 3 | MATH 150 |
| PHYS 201 | General Physics II | 4 | PHYS 200, MATH 151 | |
| EMEC/PHYS 221 | Engineering Materials | 3 | CHEM 105, PHYS 200 | |
| PHYS 301 | Classical Mechanics | 3 | PHYS 200, MATH 350 | |
| COMP 350 | Introduction to Software Engineering | 3 | COMP 232, COMP 262 | |
| MATH 350 | Differential Equations & Dynamical Systems | 3 | MATH 250 | |
| MATH 352 | Probability and Statistics | 3 | MATH 351 | |
| EMEC/PHYS 310 | Electronics | 4 | PHYS 201 | |
| EMEC 311 | Digital Systems Design | 3 | EMEC 200 | |
| EMEC 315 | Modeling of Mechatronics Systems | 3 | MATH 350 | |
| EMEC 316 | Sensors and Measurements | 3 | COMP 151, EMEC/PHYS 310 | |
| EMEC/COMP 462 | Embedded Systems | 3 | COMP 350 or consent | |
| EMEC/COMP 470 | Mobile Robotics | 3 | COMP 350, MATH 240 or consent | |
| EMEC 463 | Feedback Control Systems | 3 | MATH 240, MATH 350 | |
| EMEC 491 | Capstone Preparation | 1 | Senior standing in Mechatronics Major | |
| EMEC 499 | Capstone | 3 | Senior standing in Mechatronics Major | |
| Major | 93 | |||
| GE/AIR | 39 | |||
| Total | 132 | |||
| Optional Electives: | ||||
| EMEC 401 | Fluid Mechanics | 3 | Senior standing in Mechatronics Major | |
| EMEC/PHYS 305 | Thermal and Statistical Physics | 3 | MATH 350, PHYS 201 | |
| COMP/ART/IT 464 | Computer Graphic System and Design I | 3 | COMP 350, MATH 240 | |
student learning outcomes
We envision the following Program Learning Outcomes; our graduates will:
- Be competent engineers and problem solvers.
- Possess a high level of erudition in the field of Mechatronics Engineering.
- Have knowledge of standard engineering tools, and their application in the field.
- Be effective communicators.
- Be prepared to undertake engineering jobs in a wide variety of engineering fields.
Based on our experience, and the experience of other programs, we propose the following initial small set of Student Learning Outcomes:
- Apply knowledge of Mathematics, Science, and Engineering.
- Design experiments to evaluate the performance of a mechatronic system or component with respect to specifications.
- Design a mechatronic system, component, or process to meet desired needs.
- Define and solve an Engineering problem.
- Develop and defend a written statement of professional ethical responsibility related to their field of study.
- Ability to communicate effectively.
1 will be covered in the first two years’ science and introductory courses (programming, calculus, chemistry, physics, etc.), and rigorous logical / critical thinking will be taught in many courses, for example MATH/PHIL 230. 2, 3, 4 will be covered in multiple courses, for example Engineering Design will be taught in EMEC 225, while solving engineering problems will be taught in Mobile Robotics (EMEC/COMP 470) or Embedded Systems (EMEC/COMP 462). Communication skills will be taught in General Education courses, such as first-year writing courses.
summary of new courses
EMEC 200 – Logic Circuits: Basics of digital electronic devices and methodologies used in digital circuit design. Design, analysis and trouble shooting of logic gates, counters, registers, memory units, pulse and switching circuits, and control circuits. Comparison of digital TTL integrated circuits with other families of logic devices. Includes student projects.
EMEC/PHYS 221 – Engineering Materials: Examines the interrelationships between processing, structure, properties, and performance of various engineering materials such as metals, polymers, ceramics, composites, and semiconductors. Studies the effects of heat, stress, imperfections, and chemical environments upon material properties and performance. Emphasizes developing an ability to select appropriate materials to meet engineering design criteria.
EMEC 225 – Engineering Design: Introduction to engineering design processes, methods, and decision making using team design projects; design communication methods including graphical, verbal, and written.
EMEC 311 – Digital Systems Design: Introduces students to the design of digital systems using hardware description languages. The student will the use computer-aided design tools to design, simulate, prototype, and verify complex digital systems using programmable logic devices and field-programmable gate arrays.
EMEC 315 – Modeling of Mechatronic Systems: Introduces students to modeling techniques and analysis of mechatronic systems. Topics such as state-space and transfer function representation, linearization, and frequency domain analysis are covered. Simulation software will be utilized to quantify and visualize system performance.
EMEC 316 – Sensors and Measurements: Basic measurements with standard laboratory instruments and common sensor interfaces are introduced. Topics include the calibration, transient responses, and statistical characterization of common sensors used in mechatronic systems.
EMEC 401 – Fluid Mechanics: Principal concepts and methods of fluid mechanics are introduced. Students will learn to apply these concepts and methods to the design of fluid systems.
EMEC 463 – Feedback Control Systems: Analysis and design of feedback control systems. Topics include representing dynamical systems with transfer functions and state variables, stability and dynamic analysis using techniques from both the time and frequency domains, the design of feedback regulators and controllers, and computer aided design and analysis.
EMEC 491 – Capstone Preparation: Research and develop a proposal for a significant Mechatronics project under faculty supervision.
EMEC 499 – Capstone: Design, implement and present a significant Mechatronics project under faculty supervision.
abet accreditation
From the ABET website:
We are a nonprofit, non-governmental accrediting agency for programs in applied science, computing, engineering and engineering technology and we are recognized as an accreditor by the Council for Higher Education Accreditation.
ABET accreditation provides assurance that a college or university program meets the quality standards of the profession for which that program prepares graduates.
A scrutiny of the ABET requirements for Mechatronics shows that many of the courses required for such a degree are already being offered at CI. We have a strong offering in Computer Science, Mathematics, and Physics, and with a modicum of effort we could have a program meeting the requirements for an ABET accreditation. The main investment would be three new faculty members, and appropriate lab equipment. We have already hired a new faculty (starting date fall 2017), Houman Dallali, and we are going to hire further two new faculty. Our goal is to seek ABET accreditation within 4 to 5 years.
LAb space
 The new lab space in the Sierra Hall building opened in the fall of 2015. We have 3 general labs, and 3 dedicated labs (Robotics, Embedded Systems, and Networks & Security), as well as a tutoring center. More information about our labs can be found here: http://compsci.csuci.edu/resources/labs.htm. We are also in the process of organizing further space for our Mechatronics needs, but the current labs are well set up for the initial needs.
The new lab space in the Sierra Hall building opened in the fall of 2015. We have 3 general labs, and 3 dedicated labs (Robotics, Embedded Systems, and Networks & Security), as well as a tutoring center. More information about our labs can be found here: http://compsci.csuci.edu/resources/labs.htm. We are also in the process of organizing further space for our Mechatronics needs, but the current labs are well set up for the initial needs.
Digital Forensics and Security Toolkit to be made available online
 My student Mattias Huber presenting a tool for detecting Malware at the CSU Channel Islands Computer Science Capstone Showcase on May 11, 2017.
My student Mattias Huber presenting a tool for detecting Malware at the CSU Channel Islands Computer Science Capstone Showcase on May 11, 2017.
This tool can be used to upload a target file, directory, or URL to Virus Total, a website that scans the target with around 60 virus scanners from the industry. If the target is not already in the Virus Total database, the scan will be queued and completed shortly. As this is an asynchronous process, this tool is useful in uploading jobs, checking if jobs have completed, and displaying reports on completed jobs. The system also keeps track of all files uploaded, performs checks on already uploaded files to save bandwidth, saves all completed reports in a list, and all positive reports in a separate list.
Utilizing Amazon Web Services (AWS), Elastic Compute Cloud (EC2), and Simple Storage Service (S3), this system can be set up allow users to place files into a S3 bucket which will then be scanned automatically and user can be notified of any possible positives found.
- The User places a file they wish to scan into the S3 bucket, such as
http://mybucket.s3.amazonaws.com - A dedicated EC2 instance watches the bucket, detects the new file, and uploads the file to Virus Total.
- The EC2 instance waits until Virus Total returns a completed report.
- If any positives are found the instance notifies the user, otherwise the report is added to the completed list.
Virus total has a public API that is limited to 6 uploads per minute, but CSU Channel Islands was granted research API access which is limited to 600 uploads per minute.
Mattias is going to make this tool available for everyone through GitHub.
Capstone Showcase Spring 2017; see here for more details and here for more pictures. And click here for the presentation poster.
OLLI talk on Cybersecurity June 8 at 10:00am
Michael Soltys OLLI talk on Cybersecurity
June 8, 10:00am-12:00pm.
In Broome Library 2325
Title: Best practices for staying safe on the Internet
Abstract: The Internet enables us to do wonderful things: stay connected with family and friends (e.g., Skype), shop from the comfort of our home (e.g., Amazon), watch movies at the time of our choosing and without commercials (e.g., Netflix), and check news headlines personalized to our interests and tastes (e.g., Twitter). But all this comes with a slew of threats and dangers: like the highwaymen of old, hackers prey on vulnerable victims, without having to leave their house, and covered by a blanket of anonymity. This talk will present best practices to stay safe on the Internet, enjoy its benefits, and reduce its risks.
New paper on normalization of inconsistency indicators – to appear in Journal of Approx Reason
Authors: Waldemar W. Koczkodaj, Dominik Strzalka, Jean-Pierr Magnot, Jiri Mazurek, James Peters, Michael Soltys, Jacek Szybowski, Arturo Tozzi, Hojjat Rakhshani
Title: On normalization of inconsistency indicators in pairwise comparisons
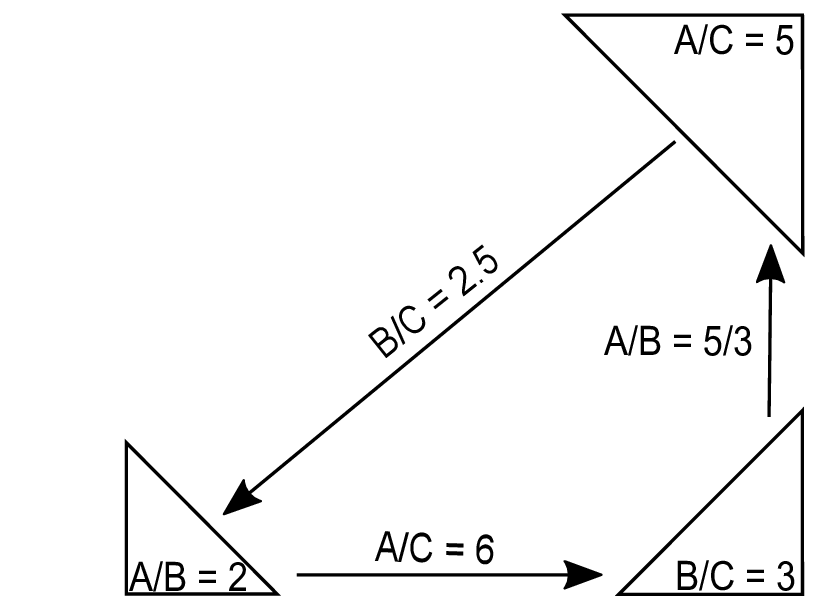 Abstract: In this study, we provide mathematical and practice-driven justification for using [0, 1] normalization of inconsistency indicators in pairwise comparisons. The need for normalization, as well as problems with the lack of normalization, are presented. A new type of paradox of infinity is described.
Abstract: In this study, we provide mathematical and practice-driven justification for using [0, 1] normalization of inconsistency indicators in pairwise comparisons. The need for normalization, as well as problems with the lack of normalization, are presented. A new type of paradox of infinity is described.
Accepted for publication in the International Journal of Approximate Reasoning, April 2017.