I am attending my first AWS re:Invent conference, Las Vegas December 2-6, 2019.
The conference is enormous, with over 60,000 attendees who command most of the big resorts on the strip.
Yesterday I participated in a Security Certification Bootcamp (proper name AWS Certification Exam Readiness: Security – Specialty) and this morning I wrote the certification exam proper; three hours long, 65 questions, and I had 3 minutes to spare at the end. Let’s face it, the exam is hard, and requires studying. I was successful, but it required steady studying over the last 3 months. The AWS certification exams are challenging, but one does learn a lot. As an academic the hardness of the exams is a good thing as it says that this material has a legitimate role to play in academia, especially as we make it accessible to our students, and deploy it toward our research.
How did I prepare? In addition to reading the requisite white papers (such as Introduction to AWS Security Processes and AWS Best Practices for DDoS Resiliency), I was fortunate enough to have access to the Cloud Guru training in security. Their 10 to 15 minute lessons in all the topics are easy to absorb, and the summaries and quizzes are a good preparation for the exam.
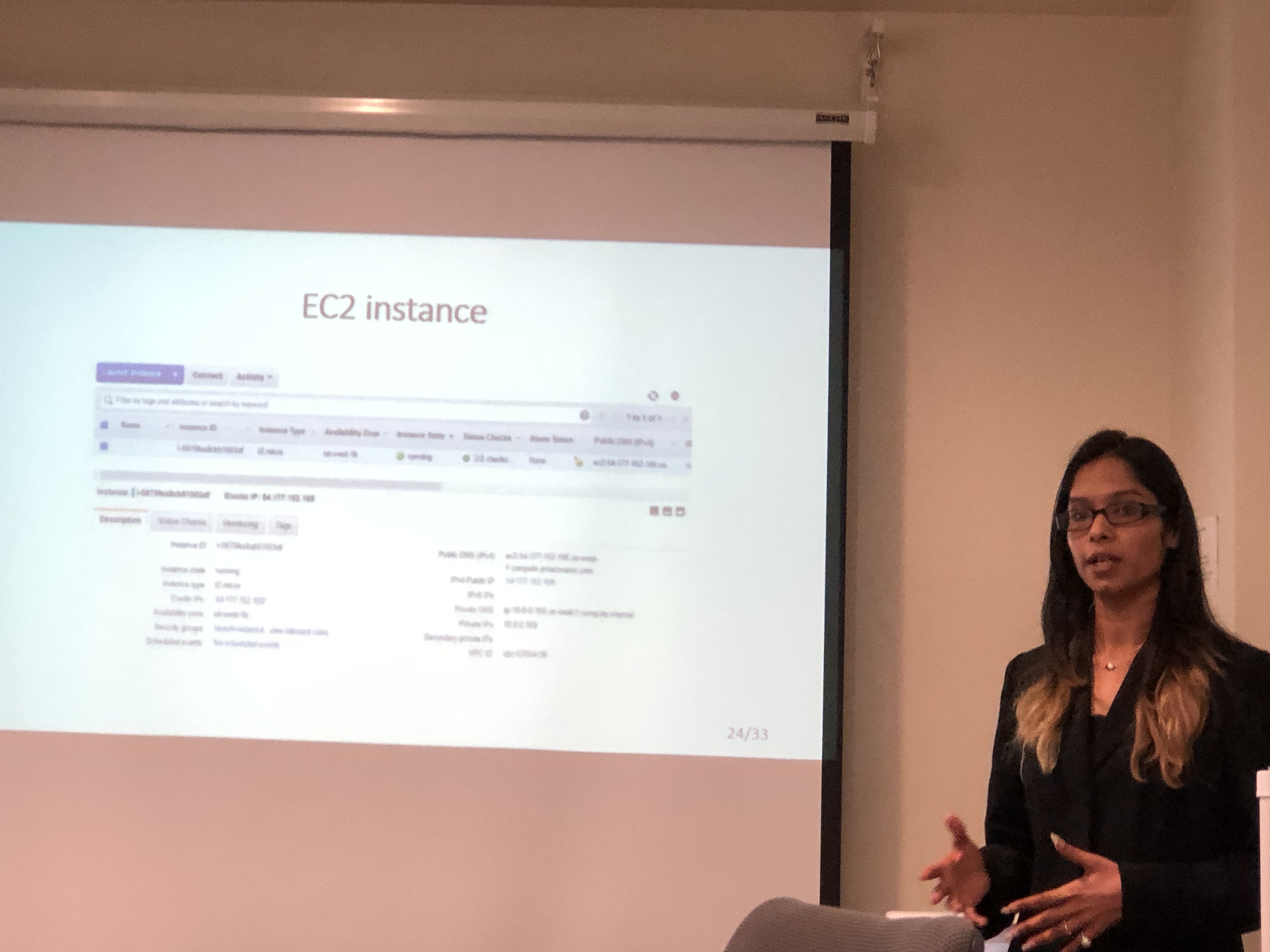
I have been teaching Cybersecurity for over a decade, but the AWS security exam is not about foundations of Cybersecurity — it is about how to use AWS tools in order to achieve security objectives; this kind of knowledge arises not from learning principles or cryptography (although that does help too!), but rather from in-depth familiarity with AWS tools, such as CloudTrail, Inspector, Macie, Athena, CloudWatch, KMS, and many many others. My plan now is to incorporate this knowledge into our CI class in Cybersecurity, COMP 524, so that students will have knowledge of fundamentals as well as an understanding of security in the (relatively new) paradigm of cloud computing. COMP 524 students will have the additional benefit of covering the content of the certification
I should also say that even though foundational knowledge such as cryptography is not tested directly, it is nevertheless helpful. For example, a good portion of the exam relates to keys, specifically AWS KMS. It is much easier to remember when symmetric keys are used (e.g., S3 encryption with AES256) rather than asymmetric keys (i.e., public keys, e.g., key pairs to SSH into EC2) when one actually understand the difference between the two. Or, for example, why hashing of encrypted logs in S3 can help with data integrity measures for backups.
The Bootcamp that I took the day before was perhaps the least helpful toward success in the exam. I would suggest to take the bootcamp at the beginning of your studies toward passing the certification exam, as a quick bird-eye overview of what needs to be mastered. I sat through the bootcamp listening to what I knew already, without the possibility of going more in depth (we had 4 hours total), and without the audience being able to ask questions, as the instructor was rushing to cover the material.
Quick Tip: AWS is uncanny in its rolling out of new tools and features, most really captivating and useful. However, keep in mind that a tool or feature that is younger than 6 months will likely not make it to the exam. As I understand, the exam process is too exacting to be done quickly, and hence it take some time before new material is incorporated.